CSIS Hoovered Location Data Without Warrant
Secret review exposes spy agency’s bulk geolocation grab—and the legal scramble that followed
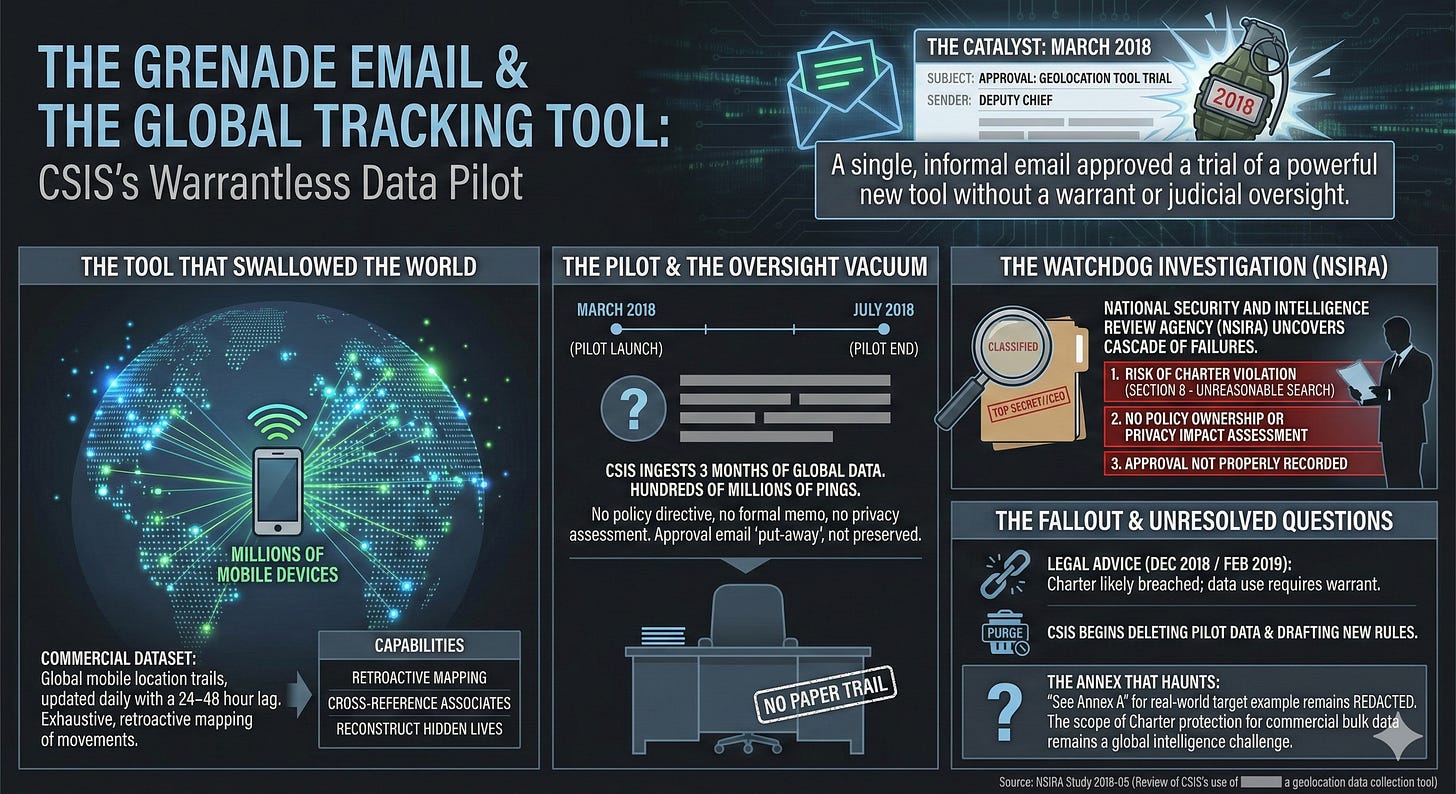
On a quiet morning in 2018, inside the fortified headquarters of Canada’s spy agency, a single email from a deputy chief landed like a grenade. It approved a trial run of a powerful new tool: a dataset that could track the movements of millions of mobile devices across the planet, updated every day, with pinpoint precision. No warrant. No judicial oversight. Just an internal nod, and CSIS began ingesting three months’ worth of global location trails—hundreds of millions of pings—into its secret servers.
This was not supposed to happen.
For over a year, the Canadian Security Intelligence Service had been quietly buying and querying what it called a “non-warranted geolocation information collection tool.” The data came commercially, lagged by 24–48 hours, and covered virtually everyone carrying a smartphone. CSIS analysts used it to retroactively map where targets had been, cross-reference associates, and reconstruct hidden lives. All of it done under the banner of “strictly necessary” national security—until the country’s newest intelligence watchdog, the National Security and Intelligence Review Agency (NSIRA), started asking questions.
What NSIRA uncovered, in a still-classified 2018 investigation stamped TOP SECRET//CEO, was a cascade of legal and policy failures that went straight to the top of the agency. The reviewers concluded there was a risk CSIS had violated section 8 of the Charter—the right to be free from unreasonable search and seizure—every single time it touched the dataset during the trial.
The Tool That Swallowed the World
The capability itself is almost cinematic in its reach.
Every time a phone checks email, loads an ad, or pings a cell tower, it leaks a breadcrumb. Aggregated by the billion and sold on the open market, those breadcrumbs become a shadow map of humanity. The particular dataset CSIS acquired (name redacted in the report) contained “three months of data” on devices worldwide, refreshed daily with a short delay. It was not real-time, but it was exhaustive.
CSIS first dipped into similar sources as far back as July 2015. By 2017 the agency was pushing hard for a formalized pilot. Internal emails show analysts salivating over the possibilities: “See Annex A for an example of the use of [redacted] against a CSIS target,” the report notes dryly.
In September 2017, as the Federal Court was quietly rewriting the rules on warrantless metadata collection in another case, CSIS lawyers were drafting briefing notes that insisted the new tool fell safely outside Charter protection. The pilot launched in March 2018. Over the next four months, the agency queried it repeatedly—exactly how many times remains blacked out.
A Deputy Chief’s Email Becomes the Smoking Gun
NSIRA’s breakthrough came from a single piece of evidence: the approval chain for the pilot.
There was no policy directive. No formal decision memo. No sign-off from any of the three directorates that were supposed to own geolocation tools. Instead, the entire authorization rested on an email exchange between senior officials and a deputy chief who simply wrote “approved.”
That email, NSIRA concluded, was “put-away” rather than preserved as an official record—a phrase that appears repeatedly in the redactions like an indictment. Without a paper trail, no one could later prove the decision had been properly vetted for lawfulness.
Worse, the briefing note used to secure that casual approval contained a critical flaw. It described two categories of data: one that supposedly met the “strictly necessary” threshold under the CSIS Act, and another that “would be” in a future situation. The legal reasoning collapsed under its own hypothetical tense.
The Legal Advice That Arrived Too Late
As the pilot hummed along, unease rippled through the agency.
In April 2018 a joint CSIS-Department of Justice briefing note declared the tool compliant. By May, a revised version went to the Director General of National Security. In July, Department of Justice lawyers were still circling the question. Only on December 7, 2018—months after the pilot ended—did formal advice land: CSIS could only use such data without a warrant in “very narrow circumstances.” The February 2019 follow-up was even blunter: the Charter had likely been breached.
By then the damage was done.
NSIRA’s final judgment was surgical. Finding no. 1: risk of section 8 violation. Finding no. 2: no policy centre owned the tool, no one assessed privacy impact, no one documented the decision. Finding no. 3: the approval itself was never properly recorded.
The Annex That Still Haunts
Buried at the back of the report sits Annex A: a real-world example of CSIS deploying the redacted tool against a live target. Every line is blacked out except the instruction to “see” it. Whatever investigators saw there was damning enough to stay classified six years later.
The implications ripple far beyond one dataset. If commercial bulk location data—bought off the shelf—can trigger Charter scrutiny, then every intelligence agency in the Five Eyes faces the same reckoning. The Americans have been through it. The British are still fighting it in court. In Canada, NSIRA simply turned over the rock and watched the light pour in.
A Quiet Purge and an Open Question
By the time the report was finalized, CSIS had already begun deleting the pilot data and drafting new retention rules. The agency told NSIRA it was “pursuing options” for any future warrant authority. Yet the central recommendation—that CSIS immediately stop using the tool and purge remaining records—hangs like an unresolved chord.
In the end, a single deputy chief’s email, a missing policy, and a dataset that mapped the world exposed the thin line Canada’s spies had been walking. The Charter, it turned out, could reach further than anyone in the room had imagined—and when the watchdog finally looked, the footprints were everywhere.
Source Documents
National Security and Intelligence Review Agency. (2018). Review of CSIS’s use of [redacted] a geolocation data collection tool (NSIRA Study 2018-05).